System Settings are accessed via the settings icon ![]() at the top right of the Management Portal.
at the top right of the Management Portal.
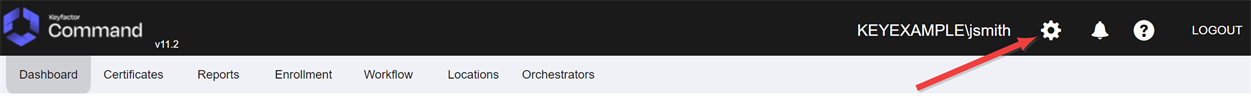
Figure 384: System Settings Icon
The options available in the System Settings section of the Management Portal are:
View or modify settings that control the Keyfactor Command applications.
Configure security roles to provide customized levels of access to the Management Portal, configure users and/or groups and grant them access to the roles.
Configure the types of certificate stores available for inventory, management, discovery, and ODKG (on-device key generation, formerly reenrollment) operations. This facilitates the creation of custom orchestrators to perform tasks against a wider set of certificate locations.
Create custom metadata![]() Metadata provides information about a piece of data. It is used to summarize basic information about data, which can make working with the data easier. In Keyfactor Command, the certificate metadata feature allows you to create custom metadata fields that allow you to tag certificates with tracking information about certificates. fields that can be used to capture additional data about certificates and report or alert based on it.
Metadata provides information about a piece of data. It is used to summarize basic information about data, which can make working with the data easier. In Keyfactor Command, the certificate metadata feature allows you to create custom metadata fields that allow you to tag certificates with tracking information about certificates. fields that can be used to capture additional data about certificates and report or alert based on it.
Display activity (e.g. creation, change, deletion) that has triggered an audit flag on a record in Keyfactor Command affecting an auditable area (e.g. Certificates, Security, Templates, Application Settings).
Configure built-in or custom event handlers.
Configure PAM![]() PAM (Privileged Access Management): Controls privileged access by vaulting credentials, enforcing least-privilege/just-in-time access, rotating secrets, and auditing sessions. Across Keyfactor products, PAM protects diverse sensitive operations and secrets—for example certificate stores and CA credentials—via built-in or third-party providers; external integrations are delivered as custom PAM extensions (several published on Keyfactor’s public GitHub). providers for use of Privileged Access Management (PAM) to secure certificate stores.
PAM (Privileged Access Management): Controls privileged access by vaulting credentials, enforcing least-privilege/just-in-time access, rotating secrets, and auditing sessions. Across Keyfactor products, PAM protects diverse sensitive operations and secrets—for example certificate stores and CA credentials—via built-in or third-party providers; external integrations are delivered as custom PAM extensions (several published on Keyfactor’s public GitHub). providers for use of Privileged Access Management (PAM) to secure certificate stores.
Configure the identity provider for Keyfactor Command.
Configure email.
View the servers on which Keyfactor Command server software is installed and the components installed on those servers.
View or change your Keyfactor Command license.
Was this page helpful? Provide Feedback