The PUT /Templates method is used to update selected information about a certificate template![]() A certificate template defines the policies and rules that a CA uses when a request for a certificate is received.. This method returns HTTP 200 OK on a success with details about the specified template.
A certificate template defines the policies and rules that a CA uses when a request for a certificate is received.. This method returns HTTP 200 OK on a success with details about the specified template.
Table 799: PUT Templates Input Parameters
| Name | In | Description | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Id | Body | Required. An integer indicating the ID of the template in Keyfactor Command. | ||||||||||
| Friendly Name | Body | A string indicating the Keyfactor Command friendly name of the template. Template friendly names, if configured, appear in the dropdowns for PFX enrollment, CSR enrollment, and CSR generation in place of the template names. This can be useful in environments where the template names are long or not very human readable. | ||||||||||
| Key Retention | Body |
A string indicating the type of key retention certificates enrolled with this template will use to store their private key in Keyfactor Command. |
||||||||||
| Key Retention Days | Body | An integer indicating the number of days a certificate’s private key will be retained in Keyfactor Command before being scheduled for deletion, if private key retention is enabled. | ||||||||||
| Key Archival | Body |
A Boolean indicating whether the template has been configured with the key archival setting in Active Directory (true) or not (false). This is a reference field and is not configurable. |
||||||||||
| Enrollment Fields | Body |
An object containing custom enrollment fields. These are configured on a per-template basis to allow you to submit custom fields with CSR enrollments and PFX enrollments to supply custom request attributes to the CA during the enrollment process. This functionality offers such benefits as:
Once created on the template, these values are shown in Keyfactor Command on the PFX and CSR enrollment pages in the Additional Enrollment Fields section. The fields are mandatory during enrollment. The data will appear on the CA / Issued Certificates attribute tab for certificates enrolled with a template configured with Keyfactor Command enrollment fields. Note: These are not metadata fields, so they are not stored in the Keyfactor Command database, but simply passed through to the CA. The CA in turn could, via a gateway or policy module, use this data to perform required actions.
For example: Copy
|
||||||||||
| Metadata Fields | Body |
An array of objects containing template-level metadata field settings. Template-level metadata field configurations can override global metadata field configurations in these possible ways:
Metadata field settings defined on a template apply to enrollments made with that template only. Template-level metadata field settings, if defined, take precedence over global-level metadata field settings. For example: Copy
|
||||||||||
| Allowed Enrollment Types | Body |
An integer indicating the type of enrollment allowed for the certificate template. Setting these options causes the template to appear in dropdowns in the corresponding section of the Management Portal. In the case of CSR Enrollment and PFX Enrollment, the templates only appear in dropdowns on the enrollment pages if they are available for enrollment from a CA also configured for enrollment within Keyfactor Command. See Adding or Modifying a CA Record for more information. |
||||||||||
| Template Regexes | Body |
An array of objects containing individual template-level regular expressions against which to validate the subject data. Regular expressions defined on a template apply to enrollments made with that template only. Template-level regular expressions, if defined, take precedence over system-wide regular expressions. For more information about system-wide regular expressions, see GET Templates Settings.
For example: Copy
|
||||||||||
| Template Defaults | Body |
An array of objects containing individual template-level template default settings. Template defaults defined on a template apply to enrollments made with that template only. Template-level defaults, if defined, take precedence over system-wide template defaults. For more information about system-wide template defaults, see GET Templates Settings. For example: Copy
|
||||||||||
| Template Policy | Body |
An object containing the individual template-level template policy settings. Template policies defined on a template apply to enrollments made with that template only. Template-level policies, if defined, take precedence over system-wide template policies. For more information about system-wide template policies, see GET Templates Settings. For example: Copy
|
||||||||||
| Use Allowed Requesters | Body | A Boolean that indicates whether the Restrict Allowed Requesters option should be enabled (true) or not (false). The Restrict Allowed Requesters option is used to select Keyfactor Command security roles that a user must belong to in order to successfully enroll for certificates in Keyfactor Command using this template. This is typically used for EJBCA templates and Microsoft templates that are not in the local Active Directory forest, since in these cases, Keyfactor Command cannot make use of the access control model of the CA itself to determine which users can enroll for certificates; this setting replaces that functionality. This setting is similar to setting request certificates for the selected security roles at the template level on a Microsoft CA. In addition to granting permissions at the template level, you need enable the Restrict Allowed Requesters option to grant permissions at the CA level. See Adding or Modifying a CA Record for more information. | ||||||||||
| Allowed Requesters | Body |
An array of strings containing the list of Keyfactor Command security roles—as strings—that have been granted enroll permission on the template. For example: Copy
|
||||||||||
| Requires Approval | Body |
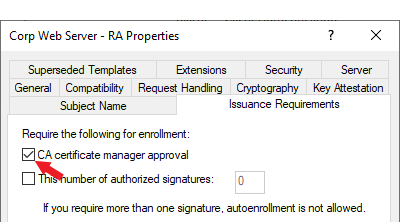
A Boolean indicating whether the template has been configured with the Microsoft CA certificate manager approval option enabled (true) or not (false). Important: Any templates that are configured on the Microsoft CA Issuance Requirements tab for CA certificate manager approval cannot be used for enrollment and associated alerting in Keyfactor Command without configuring private key retention. Any of the enabled private key retention settings (settings other than none as described for KeyRetention) will allow a template requiring manager approval to work with Keyfactor Command PFX and CSR enrollment.
Figure 458: Microsoft Issuance Requirements on a Template for Manager Approval |
||||||||||
| Key Usage | Body |
An integer indicating the total key usage of the certificate.
Key usage is stored in Active Directory as a single value made of a combination of values. For example, a value of 160 would represent a key usage of digital signature with key encipherment. A value of 224 would add nonrepudiation to those. |
||||||||||
| Allow One Click Renewals | Body | A Boolean indicating whether One-Click Renewal will be allowed for certificate renewals requested with this template (true) or not (false). If you wish to use One-Click Renewal for certificates, the Allow One-Click Renewals option must be enabled in both the templates and CAs to which you want One-Click Renewal to apply (see Certificate Template Operations and Adding or Modifying a CA Record). |
Table 800: PUT Templates Response Body
| Name | Description | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Id | An integer indicating the ID of the template in Keyfactor Command. | ||||||||||
| Common Name | A string containing the common name (short name) of the template. This name typically does not contain spaces. For a template created using a Microsoft management tool, this will be the Microsoft template name. For a template generated for an EJBCA CA, this will be built using a naming scheme of <end entity profile name>_<certificate profile name>. This field is populated based on information retrieved from the CA and is not configurable. | ||||||||||
| Template Name | A string containing the name of the template. For a template created using a Microsoft management tool, this will be the Microsoft template display name. For a template generated for an EJBCA CA, this will be built using a naming scheme of <end entity profile name> (<certificate profile name>). This field is populated based on information retrieved from the CA and is not configurable. | ||||||||||
| Oid | A string containing the object ID of the template in Active Directory. For Microsoft templates, this field is populated from Active Directory. For EJBCA templates, this field is generated within Keyfactor Command as an object identifier, but does not follow official OID conventions. The field is not configurable. | ||||||||||
| KeySize | A string indicating the minimum supported key size of the template as returned by the CA. This value is calculated based on the algorithms provided in the template from the CA (see KeyAlgorithms). The algorithm key types and sizes are evaluated in order (RSA, ECC, Ed448, and Ed25519) and from these, the minimum type and size is determined. For example, if the template supports RSA, Ed448, and Ed25519, the minimum key type will be evaluated to RSA. Then for that algorithm, the minimum key size returned by the CA will be selected (e.g. 2048 if 2048 and 4096 are returned for RSA). See the KeyAlgorithms field for the complete list of supported key sizes and types. The field is not configurable. | ||||||||||
| KeyType | A string indicating the key type of the template as returned by the CA. See details under KeySize. See the KeyAlgorithms field for the complete list of supported key sizes and types. The field is not configurable. | ||||||||||
| Forest Root |
A string indicating the forest root of the template. For Microsoft templates, this field is populated from Active Directory and is not configurable. Note: The ForestRoot has been replaced by the ConfigurationTenant from release 10, but is retained for backwards compatibility.
|
||||||||||
| Configuration Tenant | A string indicating the configuration tenant of the template. For Microsoft templates, this field is populated from Active Directory. For EJBCA templates, this field is populated from the Keyfactor Command CA record. The field is not configurable. | ||||||||||
| Friendly Name | A string indicating the Keyfactor Command friendly name of the template. Template friendly names, if configured, appear in the dropdowns for PFX enrollment, CSR enrollment, and CSR generation in place of the template names. This can be useful in environments where the template names are long or not very human readable. | ||||||||||
| Key Retention |
A string indicating the type of key retention certificates enrolled with this template will use to store their private key in Keyfactor Command. |
||||||||||
| Key Retention Days | An integer indicating the number of days a certificate’s private key will be retained in Keyfactor Command before being scheduled for deletion, if private key retention is enabled. | ||||||||||
| Key Archival |
A Boolean indicating whether the template has been configured with the key archival setting in Active Directory (true) or not (false). This is a reference field and is not configurable. |
||||||||||
| Enrollment Fields |
An object containing custom enrollment fields. These are configured on a per-template basis to allow you to submit custom fields with CSR enrollments and PFX enrollments to supply custom request attributes to the CA during the enrollment process. This functionality offers such benefits as:
Once created on the template, these values are shown in Keyfactor Command on the PFX and CSR enrollment pages in the Additional Enrollment Fields section. The fields are mandatory during enrollment. The data will appear on the CA / Issued Certificates attribute tab for certificates enrolled with a template configured with Keyfactor Command enrollment fields. Note: These are not metadata fields, so they are not stored in the Keyfactor Command database, but simply passed through to the CA. The CA in turn could, via a gateway or policy module, use this data to perform required actions.
|
||||||||||
| Metadata Fields |
An array of objects containing template-level metadata field settings. Template-level metadata field configurations can override global metadata field configurations in these possible ways:
Metadata field settings defined on a template apply to enrollments made with that template only. Template-level metadata field settings, if defined, take precedence over global-level metadata field settings. |
||||||||||
| Allowed Enrollment Types |
An integer indicating the type of enrollment allowed for the certificate template. Setting these options causes the template to appear in dropdowns in the corresponding section of the Management Portal. In the case of CSR Enrollment and PFX Enrollment, the templates only appear in dropdowns on the enrollment pages if they are available for enrollment from a CA also configured for enrollment within Keyfactor Command. See Adding or Modifying a CA Record for more information. |
||||||||||
| Template Regexes |
An array of objects containing individual template-level regular expressions against which to validate the subject data. Regular expressions defined on a template apply to enrollments made with that template only. Template-level regular expressions, if defined, take precedence over system-wide regular expressions. For more information about system-wide regular expressions, see GET Templates Settings.
|
||||||||||
| Template Defaults |
An array of objects containing individual template-level template default settings. Template defaults defined on a template apply to enrollments made with that template only. Template-level defaults, if defined, take precedence over system-wide template defaults. For more information about system-wide template defaults, see GET Templates Settings. |
||||||||||
| Template Policy |
An object containing the individual template-level template policy settings. Template policies defined on a template apply to enrollments made with that template only. Template-level policies, if defined, take precedence over system-wide template policies. For more information about system-wide template policies, see GET Templates Settings. |
||||||||||
| Key Algorithms |
An object containing the key algorithms defined for the template as reported by the CA. This information indicates all the algorithms that could possibly be supported when the template is used for enrollment. Template policy within Keyfactor Command might limit this. |
||||||||||
| Use Allowed Requesters | A Boolean that indicates whether the Restrict Allowed Requesters option should be enabled (true) or not (false). The Restrict Allowed Requesters option is used to select Keyfactor Command security roles that a user must belong to in order to successfully enroll for certificates in Keyfactor Command using this template. This is typically used for EJBCA templates and Microsoft templates that are not in the local Active Directory forest, since in these cases, Keyfactor Command cannot make use of the access control model of the CA itself to determine which users can enroll for certificates; this setting replaces that functionality. This setting is similar to setting request certificates for the selected security roles at the template level on a Microsoft CA. In addition to granting permissions at the template level, you need enable the Restrict Allowed Requesters option to grant permissions at the CA level. See Adding or Modifying a CA Record for more information. | ||||||||||
| Allowed Requesters |
An array of strings containing the list of Keyfactor Command security roles—as strings—that have been granted enroll permission on the template. |
||||||||||
| Display Name | A string indicating the Keyfactor Command display name of the template. If a template friendly name is configured, this is used as the display name. If not, the template name is used. The display name appears in the dropdowns for PFX enrollment, CSR enrollment, and CSR generation. The display name is a generated field and is not directly configurable. | ||||||||||
| RFC Enforcement | A Boolean indicating whether RFC 2818 compliance enforcement is enabled (true) or not (false). When this option is set to true, certificate enrollments made through Keyfactor Command for this template must include at least one DNS SAN. In the Keyfactor Command Management Portal, this causes the CN entered in PFX enrollment to automatically be replicated as a SAN, which the user can either change or accept. For CSR enrollment, if the CSR does not have a SAN that matches the CN, one will automatically be added to the certificate if this is set. By default, this is set to false at a system-wide level. | ||||||||||
| Requires Approval |
A Boolean indicating whether the template has been configured with the Microsoft CA certificate manager approval option enabled (true) or not (false). Important: Any templates that are configured on the Microsoft CA Issuance Requirements tab for CA certificate manager approval cannot be used for enrollment and associated alerting in Keyfactor Command without configuring private key retention. Any of the enabled private key retention settings (settings other than none as described for KeyRetention) will allow a template requiring manager approval to work with Keyfactor Command PFX and CSR enrollment.
Figure 459: Microsoft Issuance Requirements on a Template for Manager Approval |
||||||||||
| Key Usage |
An integer indicating the total key usage of the certificate.
Key usage is stored in Active Directory as a single value made of a combination of values. For example, a value of 160 would represent a key usage of digital signature with key encipherment. A value of 224 would add nonrepudiation to those. |
||||||||||
| Extended Key Usages |
An array of objects containing the extended key usage information for the template. This field is populated from the CA and is not configurable. |
||||||||||
| Curve |
A string indicating the friendly name of the elliptic curve algorithm configured for the template returned from the CA, for ECC templates. Possible values include:
If the template supports more than one curve, this field contains the minimum curve value. |
||||||||||
| Allow One Click Renewals | A Boolean indicating whether One-Click Renewal will be allowed for certificate renewals requested with this template (true) or not (false). If you wish to use One-Click Renewal for certificates, the Allow One-Click Renewals option must be enabled in both the templates and CAs to which you want One-Click Renewal to apply (see Certificate Template Operations and Adding or Modifying a CA Record). |
||||||||||
| KeyTypes | A string containing a comma-delimited list of the key sizes and types supported for the template returned from the CA as they are displayed in the Management Portal templates grid. Possible values include RSA 2048, ECC P-384, Ed25519, and Ed448. |