To edit one of the orchestrator![]() Keyfactor orchestrators perform a variety of functions, including managing certificate stores and SSH key stores. job types:
Keyfactor orchestrators perform a variety of functions, including managing certificate stores and SSH key stores. job types:
- In the Management Portal, browse to Orchestrators > Auto-Registration.
-
On the Orchestrator Auto-Registration Settings page, highlight the row in the grid of the job you want to edit and click Edit at the top of the grid or right-click the job in the grid and choose Edit from the right-click menu.
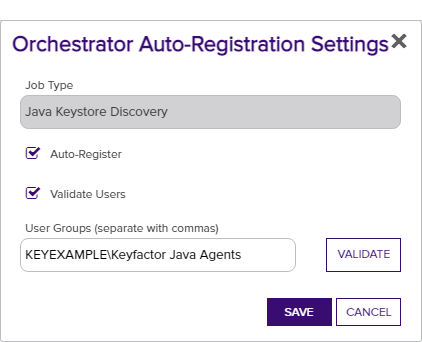
Figure 270: Orchestrator Auto-Registration Edit
- In the Orchestrator Auto-Registration Settings dialog, check the Auto-Register box if you want orchestrators to be able to auto-register. If you do not enable this, an administrator will need to visit the Orchestrator Management page in the Management Portal and manually approve each orchestrator.
-
Check the Validate Users box if you want the users under which the orchestrators are running to be a member of a specific Active Directory group in order to auto-register. If you do not enable this but you do enable auto-registration, all orchestrators will auto-register.
-
In the User Groups field, enter the AD group or groups against which to validate the user accounts in DOMAIN\group name format. Multiple groups should be separated by a comma and no space. User accounts may be used if desired.
-
Click the Validate button to validate the entered group(s).
Note: Validation is only supported on domain-joined Keyfactor Command servers. -
- Click Save.